- What important factor listed below differentiates Frame Relay from X.25?
a. Frame Relay supports multiple PVCs over a single WAN carrier connection.
b. Frame Relay is a cell-switching technology instead of a packet-switching technology like X.25.
c. Frame Relay does not provide a Committed Information Rate (CIR).
d. Frame Relay only requires a DTE on the provider side.
A. Frame Relay supports multiple private virtual circuits (PVCs), unlike X.25. It is a packet-switching technology that provides a Committed Information Rate (CIR), which is a minimum bandwidth guarantee provided by the service provider to customers. Finally, Frame Relay requires a DTE/DCE at each connection point, with the DTE providing access to the Frame Relay network, and a provider-supplied DCE, which transmits the data over the network.
- During a security assessment of a wireless network, Jim discovers that LEAP is in use on a network using WPA. What recommendation should Jim make?
a. Continue to use LEAP. It provides better security than TKIP for WPA networks.
b. Use an alternate protocol like PEAP or EAP-TLS and implement WPA2 if supported.
c. Continue to use LEAP to avoid authentication issues, but move to WPA2.
d. Use an alternate protocol like PEAP or EAP-TLS, and implement Wired Equivalent Privacy to avoid wireless security issues.
B. LEAP, the Lightweight Extensible Authentication Protocol. is a Cisco proprietary protocol designed to handle problems with TKIP. Unfortunately, LEAP has significant security issues as well and should not be used. Any modern hardware should support WPA2 and technologies like PEAP or EAP-TLS. Using WEP, the predecessor to WPA and WPA2, would be a major step back in security for any network.
- Ben has connected his laptop to his tablet PC using an 802.11g connection. What wireless network mode has he used to connect these devices?
a. Infrastructure mode
b. Wired extension mode
c. Ad hoc mode
d. Stand-alone mode
C. Ben is using ad hoc mode, which directly connects two clients. It can be easy to confuse this with stand-alone mode, which connects clients using a wireless access point, but not to wired resources like a central network. Infrastructure mode connects endpoints to a central network, not directly to each other. Finally, wired extension mode uses a wireless access point to link wireless clients to a wired network.
- Lauren’s and Nick’s PCs simultaneously send traffic by transmitting at the same time. What network term describes the range of systems on a network that could be affected by this same issue?
a. The subnet
b. The supernet
c. A collision domain
d. A broadcast domain
C. A collision domain is the set of systems that could cause a collision if they transmitted at the same time. Systems outside of a collision domain cannot cause a collision if they send at the same time. This is important, as the number of systems in a collision domain increases the likelihood of network congestion due to an increase in collisions. A broadcast domain is the set of systems that can receive a broadcast from each other. A subnet is a logical division of a network, while a supernet is made up of two or more networks.
- Sarah is manually reviewing a packet capture of TCP traffic and finds that a system is setting the RST flag in the TCP packets it sends repeatedly during a short period of time. What does this flag mean in the TCP packet header?
a. RST flags mean “Rest.” The server needs traffic to briefly pause.
b. RST flags mean “Relay-set.” The packets will be forwarded to the address set in the packet.
c. RST flags mean “Resume Standard.” Communications will resume in their normal format.
d. RST means “Reset.” The TCP session will be disconnected.
D. The RST flag is used to reset or disconnect a session. It can be resumed by restarting the connection via a new three-way handshake.
- Gary is deploying a wireless network and wants to deploy the fastest possible wireless technology. Of the 802.11 standards listed below, which is the fastest 2.4 GHz option he has?
a. 802.11a
b. 802.11g
c. 802.11n
d. 802.11ac
C. He should choose 802.11n, which supports 200+ Mbps in the 2.4 GHz or the 5 GHz frequency range. 802.11a and 802.11ac are both 5 GHz only, while 802.11g is only capable of 54 Mbps.
- What common applications are associated with each of the following TCP ports: 23, 25, 143, and 515?
a. Telnet, SFTP, NetBIOS, and LPD
b. SSH, SMTP, POP3, and ICMP
c. Telnet, SMTP, IMAP, and LPD
d. Telnet, SMTP, POP3, and X Windows
C. These common ports are important to know, although some of the protocols are becoming less common. TCP 23 is used for Telnet; TCP 25 is used for SMTP (the Simple Mail Transfer Protocol); 143 is used for IMAP, the Internet Message Access Protocol; and 515 is associated with LPD, the Line Printer Daemon protocol used to send print jobs to printers.
POP3 operates on TCP 110, SSH operates on TCP 22 (and SFTP operates over SSH), and X Windows operates on a range of ports between 6000 and 6063.
- Chris is configuring an IDS to monitor for unencrypted FTP traffic. What ports should Chris use in his configuration?
a. TCP 20 and 21
b. TCP 21 only
c. UDP port 69
d. TCP port 21 and UDP port 21
A. The File Transfer Protocol (FTP) operates on TCP ports 20 and 21. UDP port 69 is used for the Trivial File Transfer Protocol, or TFTP, while UDP port 21 is not used for any common file transfer protocol.
- FHSS, DSSS, and OFDM all use what wireless communication method that occurs over multiple frequencies simultaneously?
a. Wi-Fi
b. Spread Spectrum
c. Multiplexing
d. Orthogonal modulation
B. Frequency Hopping Spread Spectrum (FHSS), Direct Sequence Spread Spectrum (DSSS), and Orthogonal Frequency-Division Multiplexing (OFDM) all use spread spectrum techniques to transmit on more than one frequency at the same time. Neither FHSS nor DHSS uses orthogonal modulation, while multiplexing describes combining multiple signals over a shared medium of any sort. Wi-Fi may receive interference from FHSS systems but doesn’t use it.
- Which authentication protocol commonly used for PPP links encrypts both the username and password and uses a challenge/response dialog that cannot be replayed and periodically reauthenticates remote systems throughout its use in a session?
a. PAP
b. CHAP
c. EAP
d. LEAP
B. The Challenge-Handshake Authentication Protocol, or CHAP, is used by PPP servers to authenticate remote clients. It encrypts both the username and password and performs periodic reauthentication while connected using techniques to prevent replay attacks. LEAP provides reauthentication but was designed for WEP, while PAP sends passwords unencrypted. EAP is extensible and was used for PPP connections, but it doesn’t directly address the listed items.
- Which of the following options is not a common best practice for securing a wireless network?
a. Turn on WPA2.
b. Enable MAC filtering if used for a relatively small group of clients.
c. Enable SSID broadcast.
d. Separate the access point from the wired network using a firewall, thus treating it as external access.
C. SSID broadcast is typically disabled for secure networks. While this won’t stop a determined attacker, it will stop casual attempts to connect. Separating the network from other wired networks, turning on the highest level of encryption supported (like WPA2), and using MAC filtering for small groups of clients that can reasonably be managed by hand are all common best practices for wireless networks.
- What network topology is shown in the image below?
a. A ring
b. A bus
c. A star
d. A mesh

A. A ring connects all systems like points on a circle. A ring topology was used with Token Ring networks, and a token was passed between systems around the ring to allow each system to communicate. More modern networks may be described as a ring but are only physically a ring and not logically using a ring topology.
Chris is designing layered network security for his organization. Using the diagram below, answer questions 13 through 15.
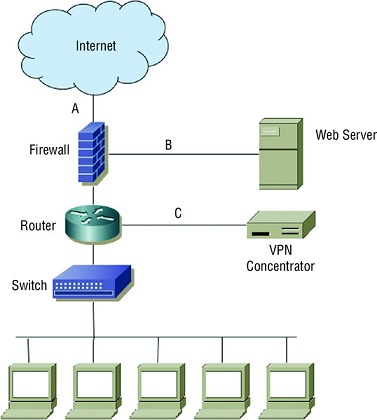
- What type of firewall design is shown in the diagram?
a. A single-tier firewall
b. A two-tier firewall
c. A three-tier firewall
d. A four-tier firewall
B. The firewall in the diagram has two protected zones behind it, making it a two-tier firewall design.
Chris is designing layered network security for his organization. Using the diagram below, answer questions 13 through 15.
- If the VPN grants remote users the same access to network and system resources as local workstations have, what security issue should Chris raise?
a. VPN users will not be able to access the web server.
b. There is no additional security issue; the VPN concentrator’s logical network location matches the logical network location of the workstations.
c. VPN bypasses the firewall, creating additional risks.
d. VPN users should only connect from managed PCs.
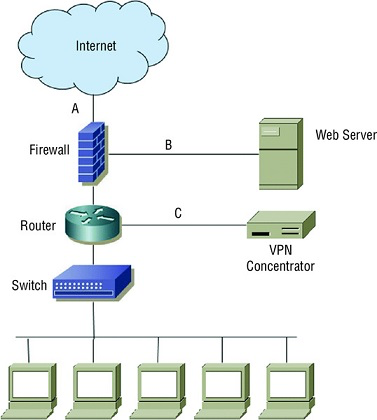
D. Remote PCs that connect to a protected network need to comply with security settings and standards that match those required for the internal network. The VPN concentrator logically places remote users in the protected zone behind the firewall, but that means that user workstations (and users) must be trusted in the same way that local workstations are.
Chris is designing layered network security for his organization. Using the diagram below, answer questions 13 through 15.
- If Chris wants to stop cross-site scripting attacks against the web server, what is the best device for this purpose, and where should he put it?
a. A firewall, location A
b. An IDS, location A
c. An IPS, location B
d. A WAF, location C
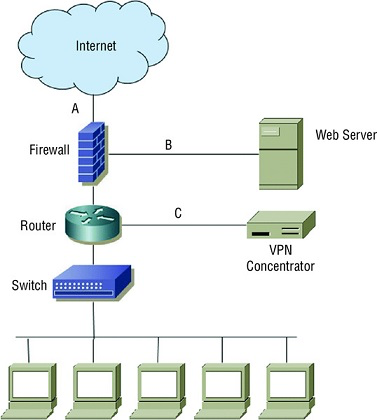
C. An intrusion protection system can scan traffic and stop both known and unknown attacks. A web application firewall, or WAF, is also a suitable technology, but placing it at location C would only protect from attacks via the organization’s VPN, which should only be used by trusted users. A firewall typically won’t have the ability to identify and stop cross-site scripting attacks, and IDS systems only monitor and don’t stop attacks.
- Susan is deploying a routing protocol that maintains a list of destination networks with metrics that include the distance in hops to them and the direction traffic should be sent to them. What type of protocol is she using?
a. A link-state protocol
b. A link-distance protocol
c. A destination metric protocol
d. A distance-vector protocol
D. Distance-vector protocols use metrics including the direction and distance in hops to remote networks to make decisions. A link-state routing protocol considers the shortest distance to a remote network. Destination metric and link-distance protocols don’t exist.
- Ben has configured his network to not broadcast a SSID. Why might Ben disable SSID broadcast, and how could his SSID be discovered?
a. Disabling SSID broadcast prevents attackers from discovering the encryption key. The SSID can be recovered from decrypted packets.
b. Disabling SSID broadcast hides networks from unauthorized personnel. The SSID can be discovered using a wireless sniffer.
c. Disabling SSID broadcast prevents issues with beacon frames. The SSID can be recovered by reconstructing the BSSID.
d. Disabling SSID broadcast helps avoid SSID conflicts. The SSID can be discovered by attempting to connect to the network.
B. Disabling SSID broadcast can help prevent unauthorized personnel from attempting to connect to the network. Since the SSID is still active, it can be discovered by using a wireless sniffer. Encryption keys are not related to SSID broadcast, beacon frames are used to broadcast the SSID, and it is possible to have multiple networks with the same SSID.
- What network tool can be used to protect the identity of clients while providing Internet access by accepting client requests, altering the source addresses of the requests, mapping requests to clients, and sending the modified requests out to their destination?
a. A gateway
b. A proxy
c. A router
d. A firewall
B. A proxy is a form of gateway that provide clients with a filtering, caching, or other service that protects their information from remote systems. A router connects networks, while a firewall uses rules to limit traffic permitted through it. A gateway translates between protocols.
19, During troubleshooting, Chris uses the nslookupcommand to check the IP address of a host he is attempting to connect to. The IP he sees in the response is not the IP that should resolve when the lookup is done. What type of attack has likely been conducted?
a. DNS spoofing
b. DNS poisoning
c. ARP spoofing
d. A Cain attack
B. DNS poisoning occurs when an attacker changes the domain name to IP address mappings of a system to redirect traffic to alternate systems. DNS spoofing occurs when an attacker sends false replies to a requesting system, beating valid replies from the actual DNS server. ARP spoofing provides a false hardware address in response to queries about an IP, and Cain & Abel is a powerful Windows hacking tool, but a Cain attack is not a specific type of attack.
- A remote access tool that copies what is displayed on a desktop PC to a remote computer is an example of what type of technology?
a. Remote node operation
b. Screen scraping
c. Remote control
d. RDP
B. Screen scrapers copy the actual screen displayed and display it at a remote location. RDP provides terminal sessions without doing screen scraping, remote node operation is the same as dial-up access, and remote control is a means of controlling a remote system (screen scraping is a specialized subset of remote control).
- Which email security solution provides two major usage modes: (1) signed messages that provide integrity, sender authentication, and nonrepudiation; and (2) an enveloped message mode that provides integrity, sender authentication, and confidentiality?
a. S/MIME
b. MOSS
c. PEM
d. DKIM
A. S/MIME supports both signed messages and a secure envelope method. While the functionality of S/MIME can be replicated with other tools, the secure envelope is an S/MIME-specific concept. MOSS, or MIME Object Security Services, and PEM can also both provide authentication, confidentiality, integrity, and nonrepudiation, while DKIM, or Domain Keys Identified Mail, is a domain validation tool.
- During a security assessment, Jim discovers that the organization he is working with uses a multilayer protocol to handle SCADA systems and recently connected the SCADA network to the rest of the organization’s production network. What concern should he raise about serial data transfers carried via TCP/IP?
a. SCADA devices that are now connected to the network can now be attacked over the network.
b. Serial data over TCP/IP cannot be encrypted.
c. Serial data cannot be carried in TCP packets.
d. TCP/IP’s throughput can allow for easy denial of service attacks against serial devices.
A. Multilayer protocols like DNP3 allow SCADA and other systems to use TCP/IP-based networks to communicate. Many SCADA devices were never designed to be exposed to a network, and adding them to a potentially insecure network can create significant risks. TLS or other encryption can be used on TCP packets, meaning that even serial data can be protected. Serial data can be carried via TCP packets because TCP packets don’t care about their content; it is simply another payload. Finally, TCP/IP does not have a specific throughput as designed, so issues with throughput are device-level issues.
- What type of key does WEP use to encrypt wireless communications?
a. An asymmetric key
b. Unique key sets for each host
c. A predefined shared static key
d. Unique asymmetric keys for each host
C. WEP has a very weak security model that relies on a single, predefined, shared static key. This means that modern attacks can break WEP encryption in less than a minute.
- An attack that causes a service to fail by exhausting all of a system’s resources is what type of attack?
a. A worm
b. A denial of service attack
c. A virus
d. A smurf attack
B. A denial of service attack is an attack that causes a service to fail or to be unavailable. Exhausting a system’s resources to cause a service to fail is a common form of denial of service attack. A worm is a self-replicating form of malware that propagates via a network, a virus is a type of malware that can copy itself to spread, and a Smurf attack is a distributed denial of service attack (DDoS) that spoofs a victim’s IP address to systems using an IP broadcast, resulting in traffic from all of those systems to the target.









