What is a firewall
Firewall: wall of bricks to prevent fire propagation
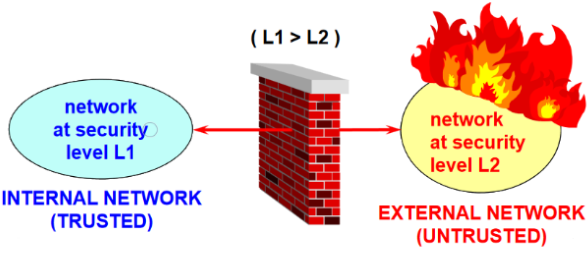
In Cyber-sec: controlled connection between networks at different security levels (networks security level -> not OSI levels). Placed at security level boundary.
Firewalls are not products that you buy, you design them.
Types:
- Ingress: filter that checks incomping connection from untrusted networks
- purpose: select the (public) services offered; limits which internal services can be accessed from the outside.
- Problem: the request to open a connection with the outside could be part of application exchange between internal users.
- Egress: checks outgoing connections
- Check personell activity: visisted websites, verify confidential documents are not sent outside network, verify user is not download malware.
- Classification is easy for channel based services(e.g. TCP, applications), difficult for message-based services ( ICMP, UDP applications), in the latter the firewall is usually bidirectional (distinction between ingress/egress meaningless).
Firewall design
Firewall are deisgned, not bought.
The design can consiste of a single component, and that’s why company say they are “offering firewalls”.
The ability to configure components gives enough freedom that we are able to achieved the desired trade-off between security and functionality at a minimum cost.
When designing a firewall, we need to understand which security level we’ll be working on.
There’s an inverse relationship between the level of functionality offered and the security level achieved.

Firewall 3 commandments
- Firewall must be the only pont of contact between internal and external network
- only “authorized” traffic can traverse the firewall: we know apriori the description of the kind of traffic
- protocols, ports, external nodes addresses
- risk of cutting off valid traffic and to loose or open for attackers.
- the FW must be a highly secure system itself: some companies use a powerful general purpose to install the firewall on, but they load other programs on it, that could impact the overall security of the system.
Authorization policies
Whitelisting: what is not explicitly permitted is prohibited.
- Difficult to manage
- higher level of security
- suggested
Blacklisting: what is not explicitly prohibited is permitted.
- Lower security (open gates)
- Easier to manage
Basic Firewall components
- Screening router (choke): router able to filter traffic at network level
- Bastion host: secure system, periodically audited, First line of defese.
- Application gateway (proxy): works on behalf of the application to handle external traffic. Has access control functionality.
- Dual-homed gateway: system with 2 network cards, acts as a bridge between two networks, but with normal routing disabled: other components should be “mounted” on it, that decide if packets are allowed or not.
Firewall name by network stack level
There are different terms used to refer to the firewall depending on the network level at which it works.
Application gateway: examines in detail application data.
Circuit Gateway: works at layer 4, TCP/UDP is the data unit used to filter traffic.
Packet filter: typically only the information about the network level is analyzed (not upper level).
The higher the level the more accurate is the detection, but the more expensive it is.

Screening router architecture
Equip switching element with filtering abilities: since it is a L3 net. device, it will be able to perform filtering based on IP and upper levels (packet filter).
Pros:
- No dedicated HW needed.
- No need to modify the applications, since it doesn’t address App. Level in anyway (no need for a proxy)
- Simple, easy, cheap and…
Cons:
- insecure solution: the kind of controls it can perform aren’t that sophisticated.
- switching element is a single point of failure, if it gets pwnd, the attacker will have full access to the system.

Dual homed gateway architecture
General called “gateway”, element that checks higher level information w.r.t. packet filter. It has 2 net. cards, routing disabled, if a packet is good it will pass from one interface tothe other.
Pros:
- Easy to implement: 2 components that check different stuff.
- Requres a bit more HW than packet filter: General purpose machine with gateway SW installed.
- Since the gateway is the fronted of the internal networkit can mask internal addresses without using NAT.
- Security in-depth: duoble line of defense.
Cons:
- Inflexible: even if traffic should be permitted in the packet filter, it must also be permitted by the gateway:
- Electronic Mail Example: it’s difficult to limit who’s the sender, so that is check by the mail server (internal to the network). The gateway would reconstruct the packet only to see that it’s not its job to check the packet.
- Large work overhead.

Screened host
Improvement of the dual-homed gateway architecture by removing the bottlenex at the gateway:
packet filter is connected to the internal network as well as the gateway. The packet filter will block all traffic that doens’t come from the bastion or that isn’t whitelisted.
Pros:
- Flexible
- In this way packets that don’t need a double check can get through immediately.
Cons:
- single point of failure.
- more expensive and complex: due to sync. of 2 systems
- only hosts/protocols passing through the bastion can be masked (unless router uses NAT)

Screened subnet architecture
Screened host suffers from single point of failure problem, here the packet filter is split doing 2 different operations:
- select permitted incoming traffic
- select traffic to be forwared to the internal network:
- acts as a bridge from intermediate network and internal one.
Once a packet is allowed by the first router it will be checked by the second and forwarded to the GW r the internal network. Note that to have true defense in-depth the routers should be from 2 different vendors, so that they are not affected by the same bugs.
The network completely decoupled from both internal and external is called DMZ, usually home to the GW, public servers (web server, remote access systems), here is the place where to put services to expose to the outside.
This solution is more expensive than others, more complex.

Screened subnet architecture V2
To reduce costs and simplify management/config often routers are replaced by 3-in-1 gateway: three-legged firewall, typically a general purpose computer, that is connected to the DMS, the internal and the external network.
Components of V1 are now SW components.
This solution is cheaper than the previous, but less secure:
- Single point of failure.
- Complexity of the GW leads to larger attack surface.
Four-legged or five-legged firewalls don’t really exist, company use the term to indicate the number of net. cards/ DMZs, that can be assigned to a different deparment of the company, isolating their traffic.
Firewall technologies
Depending on the network level, different names:
- (static) packet flter
- Stateful (dynamic) packet filter
- cuf-off proxy
- circuit-level gateway/proxy
- application-level gateway/proxy
- statefule inspection
These technologies differ in terms of:
- Controls performed (threat detection)
- Performance: different levels require different computational costs.
- Protection of the firewall O.S.: some solutions have different protections for the firewall.
- Keeping or breaking the client-server model: firewalls are between client and server, they could be transparent or could act as a proxy. Breaking the client-server model is more secure, but then the firewall will be the target of attacs.
(Static) packet filter
Available on rotuers, so that bad packets can be discarded fast, abe to check IP header and when available the transport header.
Pros:
- Application independent
- Good performance
- low cost
Cons:
- easy to fool controls (e.g. ip spoofing, fragmented packets)
- complex managing services with dynamically allocated ports (e.g. FTP)
- complex config: everything is expressed in IP, ports, protcols.
- Difficult to perfom user authentication: since we are at L3.
Stateful (dynamic) packet filter
Similar concept to packet filter, but it remembers previous packets in order to process faster new ones.
Can look inside packets for commands that indicate the ports that will be used next.
Can distinguish new connections from already open ones: packets matching open connection are forwarded without any further controls.
Better performance thanks to SMP (Symmetrical Multi-Processing) thanks to use of state tables.
Still has limitations of the packet filter.
Application level gateway
Made out of a set of proxies which inspect payload at application level.
Often requires modification to the client application and may optionally mask/renumber the internal IP addresses.
When used as part of a firewall, usual performs peer authn (usually for the egress FW).
Since the proxy understands the app. level commands, it can provide top security, e.g. buffer overflow of target application.
Forward-proxy (egress) != Reverse-proxy (ingress)
Rules may be more fine-grained and simpler w.r.t. a packet filter, because they can be expressed in application-level commands.
OS on which FW is installed may expose it to attacks.
Every application needs a specfic prox., since it will need its own commands and data:
- Delay in supporting new applications
- Heavy on computational resources: for each connection a separate process is needed, which typically will run in user mode.
- Low performance (user-mod proc.)
Using SMP may improve performance, but breaks client/server model:
- More protection for the server
- May authenticate the client
- Not trasparent to the client, the application needs config. to work with proxy.
Application-level security techniques (e.g. SSL) will prevent the gateway from inspecting traffic, for this reason there are variants of the application level gateway: transport proxy and strong application proxy.
Application Gateway Variants to handle application-level security
Due to application-level security techniques (e.g. SSL) the application GW will not be able to inspect the traffic. For this reason, there are some variants:
- Transparent proxy
- less intrusive for the client
- More work (packet rerouting + destination extraction)
- Strong application proxy (checking semantics, not syntax)
- only some commands/data are forwareded, e.g. for HTTP only allow GET and POST methods.
- According to the professor, this is the only correct option.
Circuit Level gateway
Notable example SOCKS.
Between the applcation GW and packet filter. Generic proxy, that is not application aware, that creates a transport-level circuit between client and server:
- Although it doesn’t understand in any way the payload data, it just copies TCP segments UDP datagrams (if they match access control rules) from one interface to the other.
Then it reassembles ip packets, providing protection against L3/L4 attacks. - The server won’t be target of attacks related to TCP handshake, because that doesn’t happen between client and server anymore, but between client and GW and between GW and server.
Pros:
- More server protection: that is isolated from all attacks related to
- TCP handshare
- IP fragmentation (attacker could fragment packet that performs an attack, so that the packet filter is not able to bock it)
- May authenticate the client, but requires some modifications to the app.
Cons:
- Still has many limitations of the packet filter
HTTP (forward) proxy
Typically HTTP proxy, is an HTTP server acting as a front-end and then passing requests to the real server.
Benefits|:
- Network Access Control List:
- shared cache of external pages for all internal users;
- authentication and authorization of internal users
- other control (e.g. allowed sites, transfer direction, data types)

HTTP reverse proxy
HTTP server acting as a front-end for the real-server(s) which the requests are passed to.
It can implement ACL in case it is possible to limit clients that contact the server, but usually an ingress firewall doesn’t.
It is possible to inspect content.
Benefits:
- Obfucation (no real contact with the real server, no info about it)
- SSL accelerator (with unprotected back-end connections): can be the end-point for SSL/TLS. An HSM (HW sec. module) can be placed here, so that the traffic comes in clear after TLS channel is terminated, so that it can be inspected.
- Load balances
- Web accellerator (static content cache)
- Compression
- Spoon feeding: paces the speed at which a client receives a page (acccording to its speed), offloading the application server.
Configuration: Reverse proxy should be in DMZ with servers (public). If the servers need to access internal network for data, then the reverse proxy is connected to them via VPN, but the servers now reside in the internal network; this is to avoid servers having to pass reverse proxy and firewall before accessing internal network.

Web application firewall
Module installed at a proxy (forward or reverse) to filter application traffic.
Checks: HTTP commands, header of HTTP requests/responses, content of HTTP req./res.
Most widely known is ModSecurity (open-source), plugin for Apache and NGINX. OWASP (Open Web Application Security Project) has developed specific ModSecurity Core Rule SET (CRS), containing all well-known attacks, so that ModSecurity could detect and drop these.
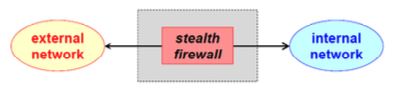
Stealth firewall
A firewall without IP address => cannot be directly attacked.
It physically intercepts packets by setting interfaces in promiscuos mode (network card gets copy of any packets reaching the interface).
Based on the security policies the firewall will discard or copy the netwrok traffic without altering it.
Since it is not addressed, it isn’t possible to make remote maintenance/config unless there is a dedicated network card attached to the security management network.
Local/personal firewall
The other firewalls suffer from sitting between 2 networks, because when HTTPS is enabled it cannot inspect packets.
The firewall, then, is now also at the ends for the HTTPS tunnel, so that packets can be inspected.
local if installed on the server.
personal if installed on the client.
It protected a single node instead of a network, usually a packet filter that limits processes that are allowed to open network channels, or to answer network requests.
In this case, we need seperate and indipendent system and firewall management, otherwise configuration problems with one or the other would not come up.
Protections offered by the firewall
If the firewall has a rule that enables some kind of traffic, and this kind of traffic can be infected (fire), then other measures are needed to protect this kind of traffic.
All channels that are enabled to pass the firewall other protections are needed: VPN, semantic firewall / IDS, Application level security.
Intrusion detection system
Major component of present security solutions: identifies actors using computer/network without authorization.
Depending on the features available, it could also detect actors violating their privileges.
IDS works based on the hypothesis that behaviour of legit users is different from the one of unauthorized users.
Stretegies:
- Passive: tries to identify signs of attack using cryptographic checksums, checking modifies files that shouldn’t have been.
- or using pattern matching: looks for specific packets, typical of the attack (attack signature)
- Active: tries to identify unknown attacks or known attacks before they produce negative result: by learning (stat. analysis and behaviour), monitoring (collection of stats.) and reacting (comparing montoring and learning)
- attacks are detected if they diverge from normal behaviour, there is always risk of undetected attacks and false positives; here human intervention is needed.
Typically IDS have both Active and passive parts.




