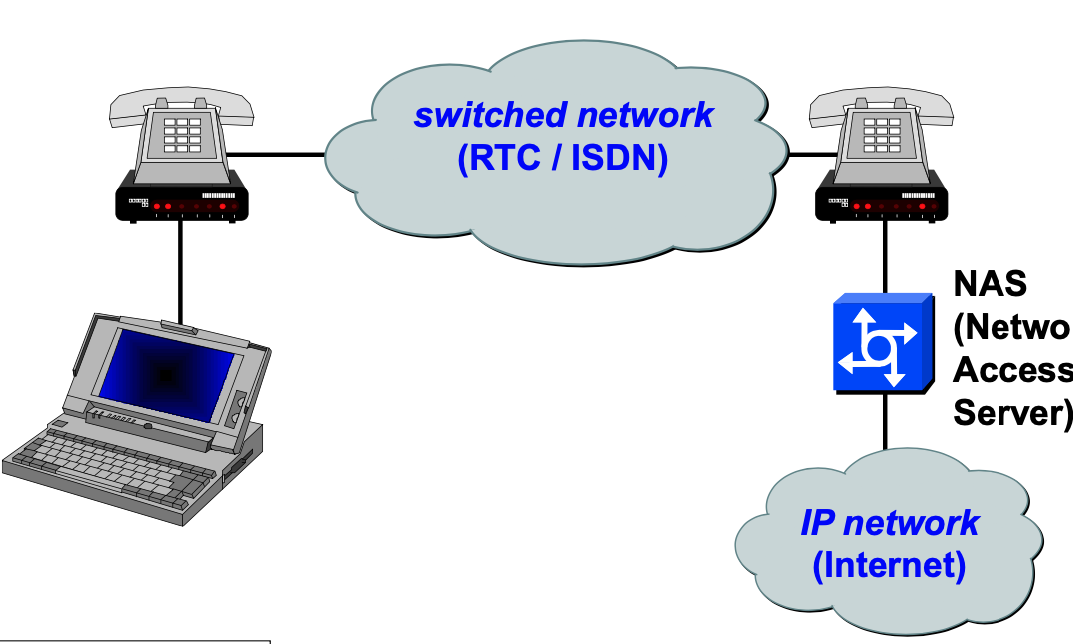
Old way: remote access (network security)
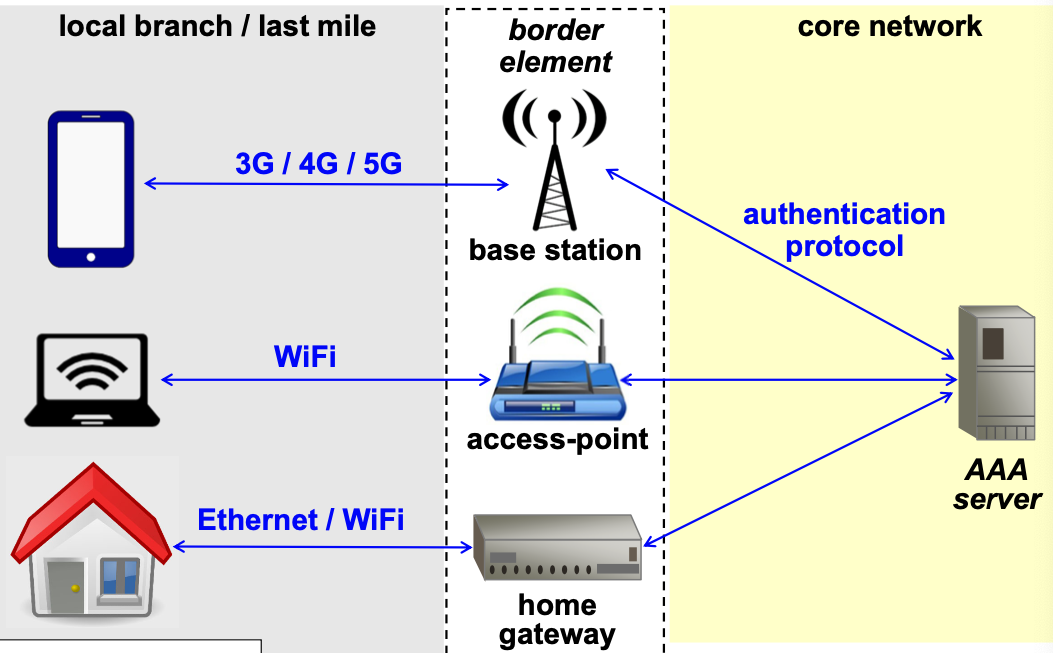
Modern network access
PPP channels authentication
PPP is a protocol to encapsulate network packets (L3, e.g. IP), and to carry the ove a point-to-point link (physical, virtual l2, virtual l3).
PPP is activated by:
- LCP (Link Control Protocol)
- (optional) authentication (PAP, CHAP or EAP)
- L3 encapsulation (e.g. IPCP, IP control protocol)
Authentication protocols for network access
- PAP (Password authentication protocol): password sent in clear
- CHAP (challenge handshake authentication protocol): symmetric challenge
- EAP ( Extensible Authentication protocol): most widely used
- uses external techniques (challenges, OTP, TLS)
EAP
This is the PPP Extensible Authentication Protocol (RFC-3748). It is a flexible L2 authentication framework. It is L2 because before getting access to internet (which is L3) you must authenticate.
Authentication mechanisms that are predefined: MD5-challenge (similar to CHAP), OTP, generic token card.
Other mechanisms can be added, examples:
- RFC-2716 PPP EAP TLS authenticaton protocol
- RFC-3579 RADIUS support for EAP
In EAP the link is not assumed to be physically secure, EAP methods must provide security (on their own), some of these methods:
- EAP-TLS
- EAP-MD5 (only EAP peer authentication, not mutual)
- EAP-TTLS (tunnelled TLS, allows any EAP method to be protected by TLS)
- EAP-SRP (secure remote password)
- GSS-API (includes KERBEROS)
When authentication doesn’t work, it doesn’t mean that it failed, there could be a network problem. Network expert is needed to understand what is the problem.
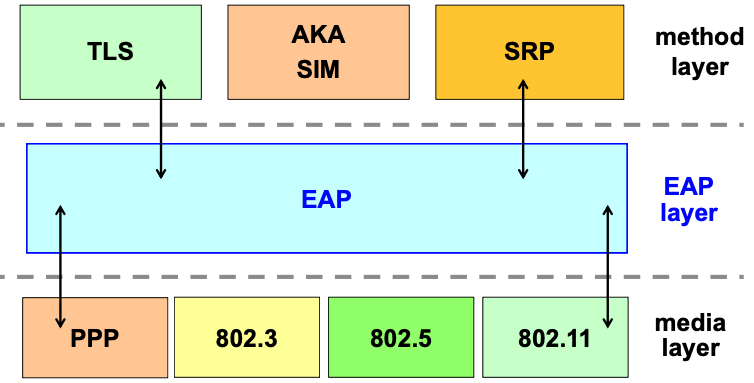
EAP encapsulation
EAP has its encapsulation protocol because it needs to transport data to perform authentication at L2 (EAP authenticates before L3):
- EAP defines some small L3 protocol that is uses; this is completely independent from IP, and it’s designed to support any link layer.
- provides ACK/NAK requires for packets, but without windowing (differently than TCP)
- assumes packets arrive in-order
- PPP guarantees it, but if EAP is being used on virtual channels like UDP or raw IP this is not guaranteed, and it wouldn’t work in that case.
- Retransmission must be guaranteed to address packet loss, after N trials the authentication fails.
- No fragmentation (depends on the MTU of underlying L2), must be taken care of by EAP methods for payload greater than minimum EAP MTU.
Authentication for network access
Authentication works like in image.
On the left communication links (modems, access points) which are terminated in a device hosted by ISP (that are controlled by the NAS).
NAS receives requests from all clients and need to check user authorization; it will use protocol on the backend IP network to ask the centralized authentication server.
NAS manufacturers claim they sec. needs three functions AAA: AuthN (check identity based on credentials), AuthZ (is entity authorized to access services?) and Accounting ( tracking resource usage, capacity analysis and billing).
Authentication server offers exactly these functionalities and communicates with NAS with 1/more protocols.
Network authentication protocols
Protocols that NAS (Network access server) and AS (Authentication server) use to communicate, main ones:
- RADIUS: it is the de-factor standard, also most used
- nice feature that allows to behave like a proxy towards other authN systems.
- Can use external AS or implement it directly.
- DIAMETER: evolution of RADIUS, has focus on roaming among different ISP; has taken better care of security (since it’s new)
- TACACS+ (TACACS, XTACACS): competitor of RADIUS, technically better, but achieved lower adoption because it’s proprietary (CISCO).
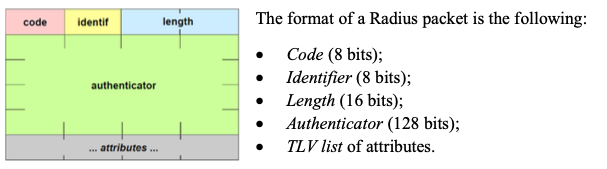
RADIUS
- Remote Authentication Dial-In User Service
- Client-server protocol between NAS and AS.
- Supports AAA (authn, authz, accounting)
- physical ports (analogical, ISDN, IEEE 802)
- virtual ports (tunnel, wireless access)
- Has centralized system for administration and accounting (to store usage data)
- 1812/UDP authn; 1813/UDP accounting
- Each transmission has time-out (UDP is unreliable); there is max. number of tries before communication is declared impossible.
- To improve performance (and resistance to DoS): allows secondary servers.
- The protocol has various extensions (includign EAP support), and it also supports 802.1X (network access security architecture);
- user auth via PAP, CHAP, token-card and EAP
- CISCO provides a free server for CryptoCard
- other support SecurID
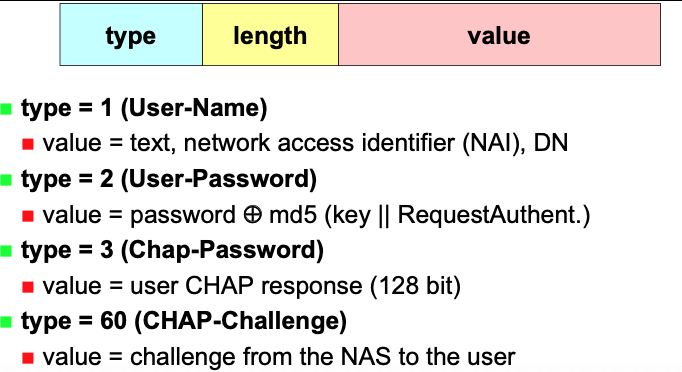
- RADIUS is extensible, attributes use TLV forma (type, length value)
RADIUS PROXY
RADIUS server can act as a proxy to authenticate with various authentication servers.
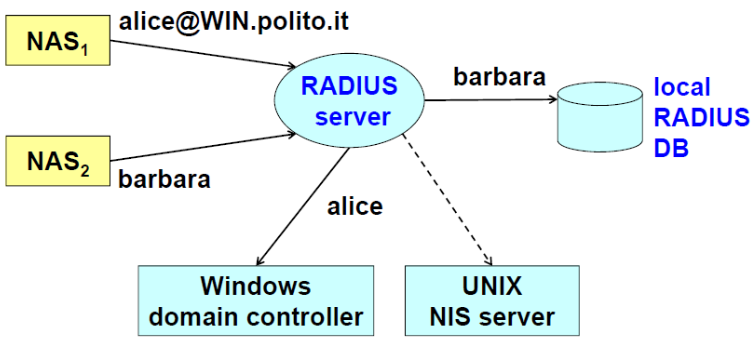
This means that RADIUS will act as a proxy for the authentication part and will redirect the request to the Windows domain controller. Then the authorization/accounting could be managed local by the RADIUS server. RADIUS can also be associated to another domain (e.g. UNIX NIS server).
Security measures needed by RADIUS
- Confidentiality, privacy
- NAS request (containing pwd) could be sniffed
- no problem with the response (can just be valid or not)
- NAS request (containing pwd) could be sniffed
- authn
- since this is UDP, an attacker could respond faster than AS, by allowing the user (even if not valid) or preventing access (even if valid) for Denial of Service.
- authn, integrity of AS resp
- otherwise it could be possible to change AS respo (y->n, n->y)
- anti-replay of AS resp
- attacker could replay AS resp (if not properly tied to NAS req)
- authN of NAS req
- otherwise an attacker could create a fake NAS and connect it to the back-end network between NAS and RADIUS server.
- availability
- DoS attacks can be performed by flooding the RADIUS server with requests coming from fake NAS.
- resistance to attack is proportional to amount of secondary servers.
- Real NAS assume that the server is busy if no response, and will switch to next one.
- DoS attacks can be performed by flooding the RADIUS server with requests coming from fake NAS.
RADIUS data protection
packet integrity and authentication via keyed-MD5:
- key = shared-secret
- client without key are ignored
password is transmitted “encrypted with MD5 (after padding with NULL bytes to a multiple of 128bit): password xor md5(key + authenticator)
RADIUS packet types
- ACCESS-REQUEST: contains credentials (username and password)
- ACCESS-REJECT: access is denied (bad username/password)
- ACCESS-CHALLENGE: requests additional information from the user (PIN, TOKEN CODE, secondary password)
- ACCESS-ACCEPT (parameters): access is granted, correlated with network parameters (e.g. IPaddr, netmask, MTU, host, port)
In each packet there is an authenticator, that has a double purpouse: in the server reply provides authentication and protection from replay, and masks the password.
- In ACCESS-REQUEST: Request Authenticator (16-byte randomly generated by NAS)
- In ACCESS-ACCEPT|REJECT|CHALLENGE: named Response authenticator, and it is computed via keyed-digest:
- md5 (code || ID || length || RequestAuth || attributes || secret)
NAI
Network Address Identifier: used to distinguish user requests made by local users or ones belonging to different security domains.
Syntax: user@realm
Rules say all devices must support NAI up to 72 bytes long.
All ASCII CHARACTERS < 128 ARE ALLOED.
username is the one used in PPP authentication phase, used when opening connection, not necessarily related to application username.
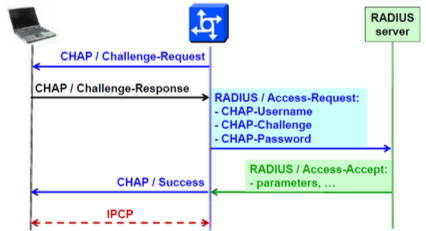
CHAP + RADIUS Example
The NAS is sending a CHAP packet containing a challenge request.
The client will sent the password through a challenge response, the the NAS will then create a RADIUS / ACCESS-REQUEST packet containing all necessary CHAP info.
RADIUS Server will answer with RADIUS / ACCESS-ACCEPT|REJECT, then the NAS will send the equivalent CHAP message.
NAS here is translating dialog between client and RADIUS server.
Then L3 will be enabled.
RADIUS ASSUMES WE ARE INSIDE A NETWORK ACCESS SYSTEM FOR A SINGLE PROVIDER.
DIAMETER
- evol. of radius
- special enphasis on roaming between ISP
- Better security w.r.t. RADIUS
- client must support IPsec and may support TLS
- server must support IPsec and TLS
- compulsory configs:
- (IPsec) ESP with non-null algo for both authentication and privacy
- (TLS) mutual authentication (client must have public-key certificate)
- (TLS) Must support RSA+RC4_128/3DES + MD5/SHA1 and may support RSA+AES_128+SHA1
IEEE 802.1X
General standard architecture based on RADIUS and DIAMETER. (authentication framework that supports multiple authentication methods)
Port-based Network access control:
- L2 authentication architecture
- usefule in wired network to block access
- absolutely needed in wireless networks (wifi is accessible from the outside)
- authentication and key management framework
- uses standard algos for key derivation (e.g. TLS, SRP)
- optional security services (authentication or authn + encryption)
- may derive session keys to use in packet authentication/integrity/confidentiality.
In picture: supplicant over wireless or lan, ask to connect to access points (authenticator, or etherNAS). When the authenticator receives EAP request, it will verify credenttials performing encapsulation/decapsulation of the packet into another protocol.
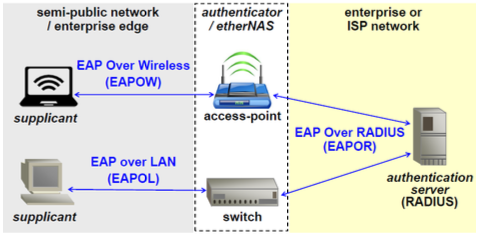
802.1X advantages
Exploits applicaiton level for the implementation of the security mechanisms, there is direct interaction between supplicant and Authentication Server, so the client are talking directly with the RADIUS/DIAMETER server.
The NAS and the network card on the other hand, now operate as a pass-through-device (encaps/decaps). This is important, because the security architecture doesn’t need to be changes with future evolution of authN techniques.
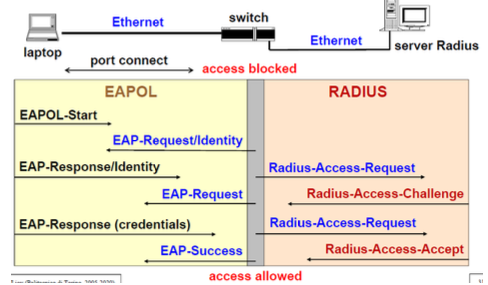
802.1X messages: example of connection
The switch acts like a pass-through element.
- The supplicant starts a negotiation by means of EAPOL-Start.
- The response from the switch is the EAP- Request/Identity and the Supplicant provides with the EAP- Response/Identity his identity, which is relayed to the Radius Server (Radius- Access-Request).
- RADIUS server will sent RADIUS-ACCESS-CHALLENGE tha will be translated in EAP-Request.
- At the end the user will be able to access the L3 network if authn works out.
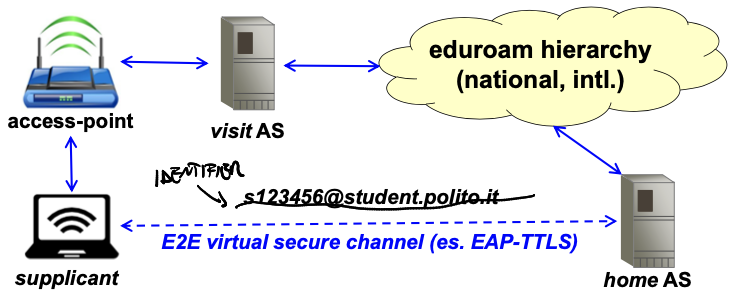
Eduroam example
Eduroam is a world-wide a RADIUS network, involves universities and research centers allover the world.
Since it will be using that Network Access Identifier (NAI) syntax, the supplicant will use his identifier (e.g. s123456@studenti.polito.it) and the local Radius Server will know that it has to go through the Eduroam hierarchy (national, international,…) until it reaches the Radius AS in which the supplicant has created his credentials (e.g. the PoliTO Radius Server), which is called Home AS.
Once it has been found, there will be a direct connection through an E2E (End-to-end) virtual secure channel (e.g. EAP-TTLS) between the supplicant and the Home AS to perform authN and then the latter will provide the answer to the access point, which will permit to the user to navigate.
Which is the best OSI level to implement security?
“Presentation” is the only one in which security measures are not useful.
Unfortunately, there is not a single optimal level.
The upper we go in the stack, the more specific can be our security function.
If the functions are placed at application level only, attacks at lower levels are possible (in particular, DoS attacks are available).
The lower we go in the stack, faster we can “expel” the intruders, but the fewer are the data for the decision.
DHCP security
DHCP (in)security:
- When L3 is reached, DHCP is one of the first things to be activated, since the client needs to know network parameter to access the network.
- But the protocol is non-authenticated and broadcast, the protocol provides address, netmask, default gateway, localnameserver and local DNS suffix.
- Making fake DHCP servers is trivial, since it works as L2 broadcast frame, attacker just needs to stay in the broadcast domain of the victing and sniff the DHCP request.
Possible attacks:
- DOS: providing wrong network configuration
- Logical (MITM): valid ip address is provided to victing, but subnet has size of 1 (netmask has only last two bits to 0), attacker ip is set as default gateway. This way victim maching is isolated, and in order to communicate with the outside it needs to go though the attacker.
- replies could reach directly the victim, but the attacker could set up a NAT to be able to receive replies too.
- Malicious name-address translation: attacker declars itself the local name server. The user then will get the addresses the attacker wants him to see. (used for phishing and pharming)
Manufacturers have tried to provide sec. improvements:
- DHCP snooping: accepts only replies from trusted ports.
- IP guard: provides room only for ip addresses got from a valid DHCP server (issue: limited number of recognied addresses)
- RFC-3118 “AuthN for DHCP messages) which uses HMAC-MD5 to authenticate the messages.
- rarely adopted because a symmetric key needs to be installed in each machine that needs to use DHCP.
- key distribution problem
- key management problem (what if a key is captured in some way?)
- rarely adopted because a symmetric key needs to be installed in each machine that needs to use DHCP.
Network Level Secuirty (L3)
Since it is the first layer to offer end-to-end connectivity, it allows end-to-end protection for L3-homogenous networks.
If end-to-end encryption is provided, then data are secured as soon as they exit from client/server, and it’s not important if routers are not properly managed, or if network is unsecure, because data are protected as soon as they exit the network interface.
For these reasons, L3 security allows to forget about all other attacks at network level, but DoS (attacket could still take out the network).
VPN
A way (HW or SW enabled) to create a private network… while using shared/untrusted channels and transmission devices. You as a company don’t have to lay cables for your private network.
Techniques:
- via private addressing
- via protected routing (IP tunnel)
- via cryptographic protection

































