Why security is important?
- Information systems can be attacked without attackers being physically present
- Consequences:
- Financial loss: money stolen or value of shares decreased or fines by authorities
- Recovery cost: making the system operational again and improving it to avoid attacks is costly
- Productivity loss: all processed are stopped to deal with the security issue → no more product features.
- Business disrution: lack of trust in the company, users may want to choose a competitor or may have to use a competitor since the company product could be unsable for some time.
Complexity is the enemy of security
- FIRST AXIOM OF ENGINEERING: The more complex a system is, the more difficult its correctness verification will be (implementation, management, operation)
- Since the current ICT scenario is full of interconnected products we are not very well positioned on the security side of things.
Keep It Simple Stupid
Definition: ICT security
- Set of products, services, organizational rules and behaviours that protect ICT systems.
- Has duty to offer these characteristics to the system (C.I.A.)
- protected from undesired access (Cofidentiality)
- guarantee privacy of information (Integrity)
- ensure service operation and availability even in unpredictable circumstance. (Availability)
Risk estimation
- Understand the assets needed for a service to work:
- Data, human resources, ICT resources, location
- Asses the vulnerabilities associated with each asset:
- weak passwords, location sensible to flooding, corruptible humans, non-encrypted data
- Vulnerabilities that are not mitigated become a security threat to the service.
- An attack is the occurrece of a threat that is deliberate.
- An event is the occurence of a threat that is accidental.
The risk is estimated by considering the impact of an event/attack and the probability of that event/attack happening.
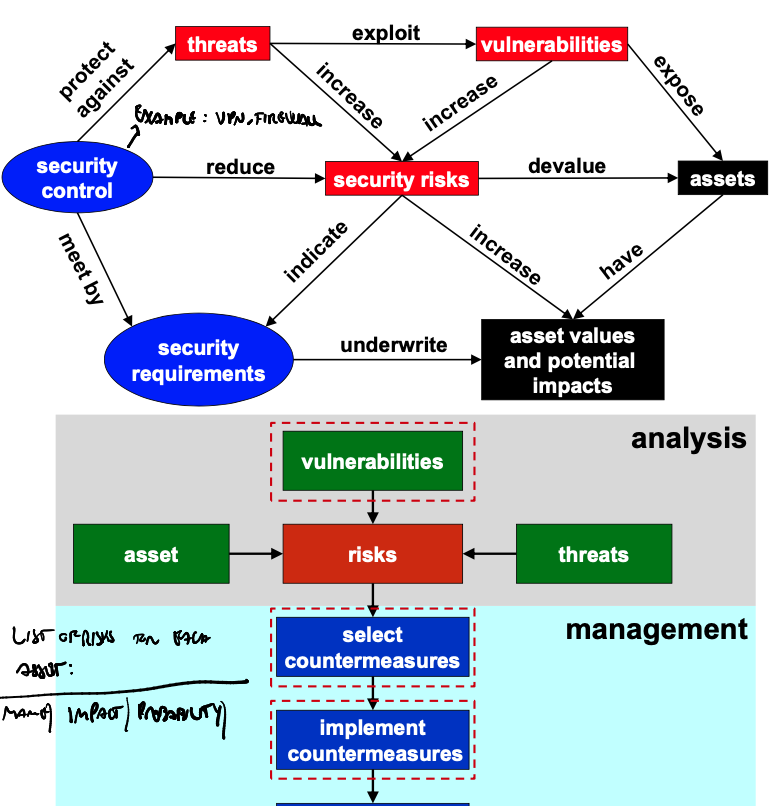
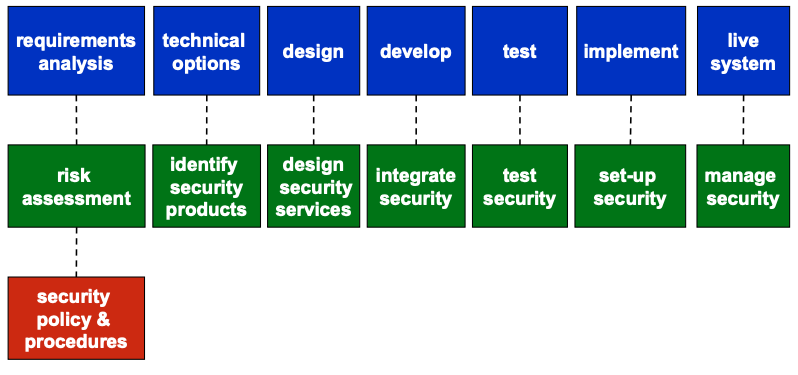
System development lifecycle | Security Dev. lifecycle
Security must be addressed at each step of the development.
Definition: Incident
A security event that compromises integrity, confidentiality or availability of an information asset.
Definition: Breach
(Data) breach: an incident tha exposes or potentially exposes data.
Definition: Disclosure
(Data) disclosure: a breach with confirmation that the data was disclosed by an unauthorized party. (Another entity has the data an knows it
Definition: Window of Exposure (WoE)
The period from the discovery of the vulnerability to the installation of the protection measure.
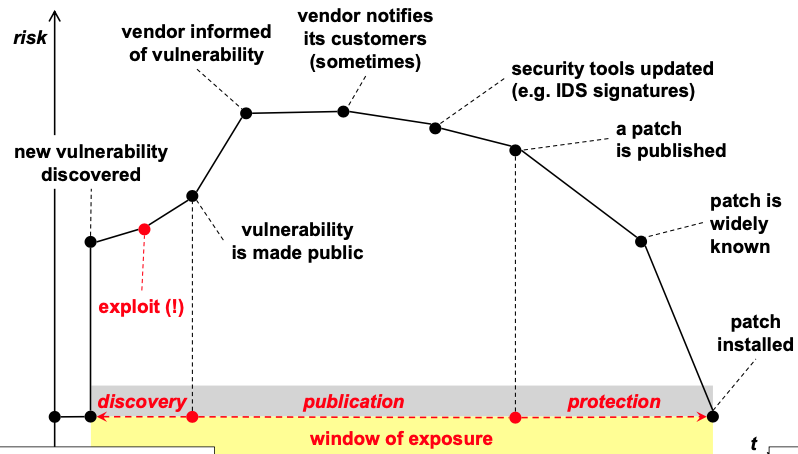
WoE: responsible disclosure
Security researchers will wait for some days to make public a vulnerability to make sure the developer can fix the vulnerability.
Example of flow:
- Sec. res. reports vulnerability to vendor; vendor acknowledges report.
- Vendor verified reproducibility, and confirms it with sec. res.
- Vendor reports an issue with the fix and that the fix might not make it to production before the vulnerability disclousure deadline.
- Sec. res. cautions potential 0-day.
- Vendor confirms the vulnerability will not be patched before deadline.
- Sec. res. confirms the intention to 0-day on the date of the deadline.
Bruce Schneier on Computer Security: Will We Ever Learn?
- Computer security flaws are inevitable.
- Systems break, vulnerabilities are reported to the press.
- People put faith in the future: this time is different, the next release will fix all problems.
- Key takeaway: security is a process, not a product: processes that are put in place to rocognize insecurities will do so.
- The trick is to reduce your risk of exposure regardless of the products or patches.
Security principles:
- Security in-depth
- Security by design
- Security by default
- Least privilege
- Need-to-know
Security in-depth
Do not rely on a single protection, if that fails you are vulnerable. Put in place secondary measures.
Security by design
Start the project/feature with security in mind. Build the project/feature around security.
Don’t add security at the end or “if there’s time.”
Least privilege
Assign to the entity that needs privileges the lowest one that allows it to achives its task.
Need-to-kwow
Similar to least privilege. Only show/transmit the data that the entity strictly-needs to accomplish the task it requested the data for.
Security by default
Allow security options by default.
E.g. users have to opt-out of security features if they don’t want them.
European Central Bank security recommendations
- These recommendations apply to:
- Payment schemes governance authorities
- payment services providers
- merchants
- Recommendations:
- Use strong customer authentication to protect internet payment initiation and sensitive payment data.
- Limit number of log-in/auth. attempts, define rules for internet payment services session “time out” and set time limits for validity of authentication.
- Establish transaction tracking to:
- prevent
- detect
- and block fraudolent transactions.
- Provide assistance and guidance to customers about security best practices; set up alerts and provide tools to monitor transactions.
Security Properties:
- Authentication (simple/mutual)
- Peer authentication
- Data / origin authentication
- Authorization, control access
- Integrity
- Confidentiality, privacy, secrecy
- Non repudiation
- Availability
- Traceability, accountability
Peer authentication
Only one entity asks for proof of authentication.
Example: computer asks username/password to user.
User doesn’t ask the computer to authenticate itself.
Mutual authentication
Mutual authentication or two-way authentication refers to two parties authenticating each other at the same time, being a default mode of authentication in some protocols.
Data authentication
Data authentication is the process of confirming the origin and integrity of data.
Non repudiation
Non-repudiation refers to a situation where a statement’s author cannot successfully dispute its authorship or the validity of an associated contract.
In digital security, non-repudiation means:
- A service that provides proof of the integrity and origin of data.
- An authentication that can be said to be genuine with high confidence.
Authorization
The system must be able to ask the following question and gives itself an answer:
does the following entity have permission to do what it’s asking me to do?
Example: can Barbara borrow Alice’s car?







